Lesson
Plan Title: How to
Perform Log Spoofing.
Concept /
Topic To Teach:
This lesson
teaches attempts to fool the human eye.
How the
attacks works: The attack
is based on fooling the human eye in log files. An attacker can erase his
traces from the logs using this attack.
General
Goal(s):
The
grey area below represents what is going to be logged in the web server's log
file.
Your goal is to make it like a username "admin" has succeeded into
logging in.
Elevate your attack by adding a script to the log file.
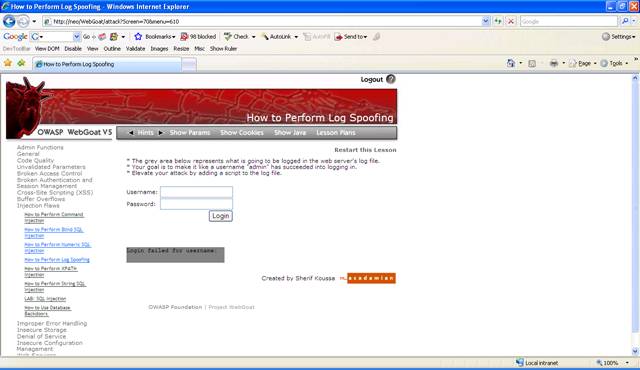
Figure 1 Log Spoofing
Solution:
This lesson accepts any input for a username and appends the information
to the log file.
Enter for username the text: smith Login Succeeded for username admin
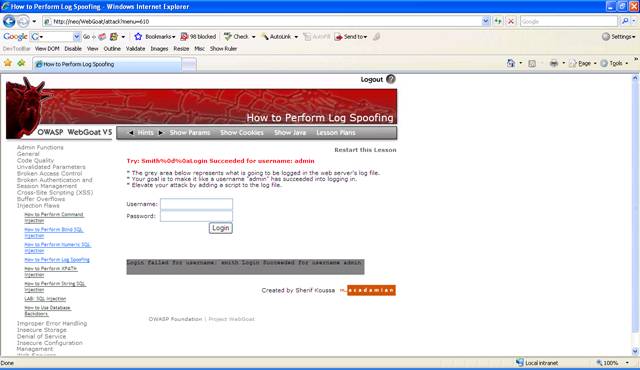
Figure 2 Log spoof with long text
The text is added to the same line, not a new line. But any input is
allowed.
In this way you can inject carriage return (%0d) and line feed (%0a) to
the application.
Fill out the following text for the username: Smith%0d%0aLogin Succeeded
for username: admin
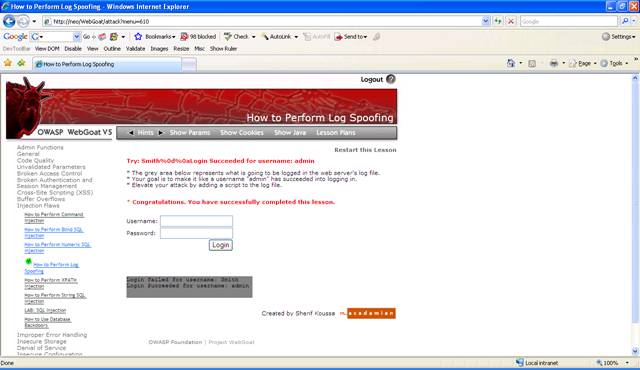
Figure 3 Lesson completed
An attacker
can use this attack to add malicious JavaScript to the log file, which will be
viewed by the administrator using a browser. What happens when you inject admin
<script>alert(document.cookie)</script> for the username?
